Surveillance surfing
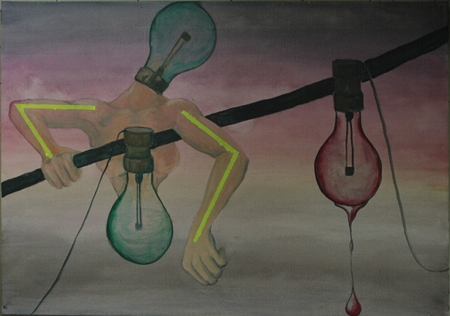
Glowlum tapping along a dull wire, artwork by Hucky Finn, oil on canvas, inspired by a photography by Baertels, www.plainpicture.com.
There have been quite some discussions here in Germany about the revelations about the surveillance of ordinary citizens and the protection of ordinary citizens data in general.
In Germany there is of course – due to its historical experiences – a different sensitivity and awareness towards this issue (There are some posts and comments here on this blog related to historical topics of control and surveillance via german secret services and other organisations like the STASI or the SS or GESTAPO (like here, here or here) and you should feel encouraged to compare the given circumstances with historical circumstances.)
Like there are discussions wether to invite Edward Snowden as a witness and wether to grant him political asylum. (He is a former employee of the american secret service, who leaked a lot of documents which give an insight into current practices of some major western secret services and partially also in corporate surveillance.) As far as I had understood this is currently however not seen as an option by politicians in power.
There are discussions about privacy and data protection in the context of the new EU-data protection regulations, which seem to be impeded by some german politicians.
There are many discussions and offers about how to privately enforce data protection and privacy, like via better encryption, detection of eventual encryption back doors etc. Some people talk already about an encryption-vs-data-snatching arms race and given all that it doesn’t sound too far fetched that we may eventually soon see robber barons (a medieval counterpart is eg. described here) who may offer data protection in exchange for massive tolls.
A rather distinct part of cryptography is the socalled quantum cryptography which is using quantum mechanics for encryption, processing and communication. Quantum cryptography had already been mentioned in this randform post. As indicated in this post a very different feature of quantum cryptography -in contrast to the usual classical cryptography- is the possibility of a kind of “sealed” key transmission. That is there are quantum communication schemes which allow to detect wether a communication had been “wiretapped” or not (i.e. as if a kind of “seal” was visibly broken). That is if you transmit a key you may notice that you had been wiretapped and hence the transmitted key should better not further be used. The key distribution can be even done within networks. The Wikipedia article about Quantum key distribution lists already some Quantum key distribution networks.
Moreover there is even intense research for optical fiber quantum networks or here in a cooperation with China even some research for using quantum communication in space, that is Vienna contributes here the base station on ground and China the satellite for quantum communication:
“Mit dem ‘Quantum Space’-Projekt bauen die heimischen Wissenschaftler des IQOQI Wien ihre international anerkannte Spitzenposition weiter aus und demonstrieren eindrucksvoll ihre Attraktivität für China”, betont der Minister.
(translation without guarantee: “With the ‘quantum space’ project scientist of the IQOQI Vienna strengthen their top position and demonstrate their attractivity for China,” emphasized the minister.)
Sofar the technology for quantum communication is rather expensive and thus in particular not really usable by ordinary citizens as means of enforcing their data protection. And there is still in principle the possibility of ultra-fast quantum computers, which may alone by their mere computing power crack current encryption standards (a randform post and some updates on this by Scott Aaronson.)
In short – one eventually may fear that we sofar saw only the tip of an iceberg, when it comes to the question of en/de-cryption armament.